Few weeks ago, one particular large scale cyber-attack hit the mainstream news everywhere. Russian cyber actor APT28 attacked SOHO routers and managed to compromise some credentials through that. The attack itself was carried in multiple phases and was quite interesting. Let’s take a look at those individual steps, what happened, how it worked and what could have been done to prevent this type of attack.
Crashing BIRD 3 by sending a Notification (CVE-2025-59688)
Over July and August, we received several reports about always the same cryptic bug happening quite sparsely. We were methodically disproving every hypothesis about this bug and slowly accepting our feat of creating a very specific and complex test setup to reproduce andproperly analyze the bug.
On the Drawbacks, Weaknesses and Appropriate Uses of NSEC3
Let’s start with a brief reminder of non-existence proofs in DNSSEC. If you have a solid understanding of the topic, feel free to skip this introduction.
The standard DNSSEC solution to proving a record’s non-existence is the NSEC RR. It contains the next node in the lexicographical order and a bitmask of available RTYPEs:
Sentinel View report – September 2023
On the first pages of the Report, we can see that September numbers are very comparable to August data. Iran-based attackers moved away from top charts, and we see that addresses from the United States now take the lead in the HTTP minipot incidents records.
The 20th annual Safer Internet Day – a look back
Safer Internet Day is celebrated in more than 180 countries around the world, always on the second Tuesday of February. This year, this day fell on February 7 and was celebrated for the 20th time. The coordinator of this day for the Czech Republic is the National Safer Internet Center, managed by the CZ.NIC Association.
Why we improve e-mail security and why it may break message redirection
In the Turris project, we are currently improving e-mail communication security. If you use our infrastructure for sending notifications from Turris devices, it also applies to you. It strengthens your protection but may “break” the redirection of messages to another address.
NXNSAttack: upgrade resolvers to stop new kind of random subdomain attack
This article describes NXNSAttack, a newly discovered DNS protocol vulnerability which affects most recursive DNS resolvers. It allows to execute random subdomain attack using DNS delegation mechanism, resulting in big packet amplification factor.
“Critical” opkg CVE and Turris
You might have heard on some news sites about “critical” vulnerability in OpenWrt. You might be worried about how it affects is your Turris. That is the reason for quotes around the word critical. TLDR not applicable against Turris
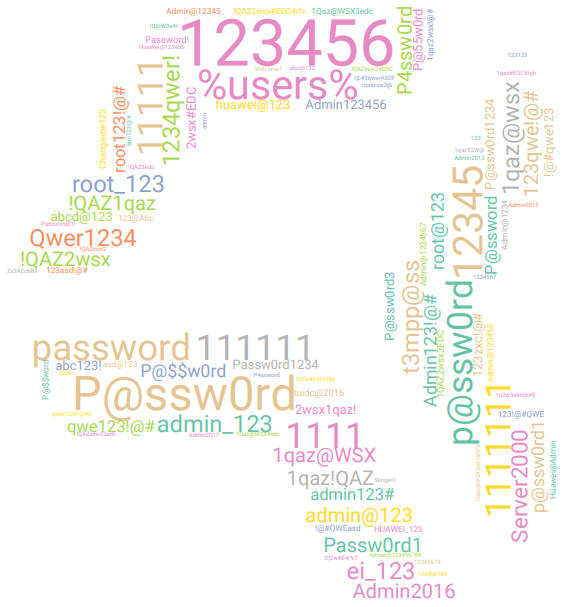
Protecting your servers with Turris Sentinel
Little bit of history
Apart from operating .CZ top level domain, CZ.NIC does a lot of other interesting things contributing to the common good. Part of it is running Czech national CSIRT team, doing security research and raising awareness about potential security issues. As part of our security research, we started wondering a long time ago how much are the average Joes and Janes attacked, by who and how. People that are just connected to the internet, run no public service and are just consumers. If only there was some kind of probe that would allow us to see what is going on there…
Digital Footprint: on-line course for children in the Czech Republic
In September this year, the Czech Safer Internet Centre (CZ.NIC), in cooperation with the National Cyber and Information Security Authority, presented an online course called Digital Footprint, intended primarily for children aged 10-13. This interactive game focuses on Internet privacy and associated socio-pathological phenomena such as personal data abuse, sexting, digital privacy or cyberbullying.