It took us really long time to release Turris OS 7.0, but it is finally out now. The only change in this release is a switch to a newer OpenWrt – namely 22.03. We are not introducing any new features (although we are for the first time using “Staging Updates“). We are even sticking with iptables for now, although upstream has moved towards nftables. All that to minimize impact on our users and provide smooth update experience. That was also part of the reason why it took so long. We tested it over and over again, fixed the issues we found and started with the tests from scratch again. Sometimes we found our feature not working, sometimes we encountered some problems with state of the upstream distribution we had to help to fix. But finally we got into state where we could release it and we did exactly that.
Sentinel View report – October 2023
An interesting dynamic is happening at the top of the attackers’ chart. First of all, Iranian attacks were overshadowed by other countries to the degree that we no longer see them in higher positions. To mention the current top four most significant, we would highlight Romania, Germany, Bulgaria, and the Netherlands. There had been consistent attacks from Germany that came into prominence about the 4th of October and then slowly started to disappear on the 16th until the final dissolution on the 18th of October. The graph line for German attacks looks very stable and consistent. On the other hand, Romania’s malicious activity, which took the top of the charts, looked erratic and unorganized in the graph. To the degree that Sentinel View graphs in the Incidents section, except for Top countries by recorded incidents, are rendered almost useless.
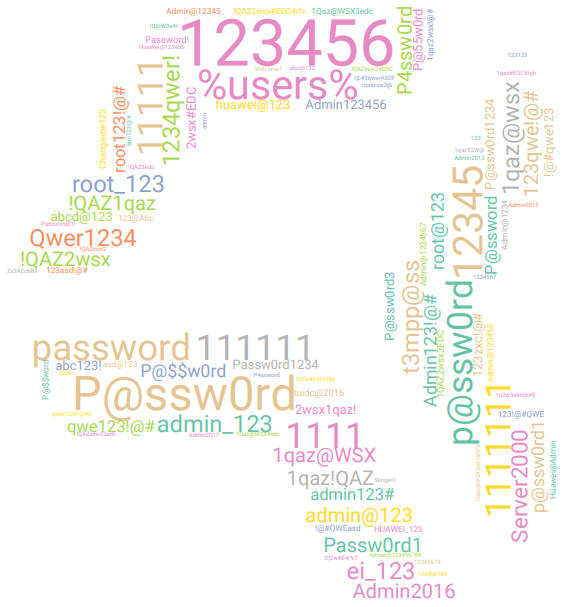
Sentinel View report – September 2023
On the first pages of the Report, we can see that September numbers are very comparable to August data. Iran-based attackers moved away from top charts, and we see that addresses from the United States now take the lead in the HTTP minipot incidents records.
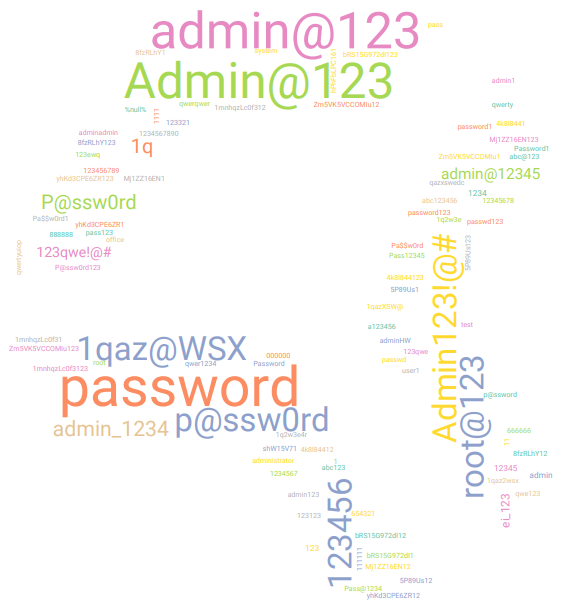
Sentinel View report – July 2023
Number of individual attackers had risen and minipot attacks doubled. Last month only three of the top attackers emerged from subnet 46.148.40.0/24, yet this month the majority of all attackers came from this Iraq subnet.
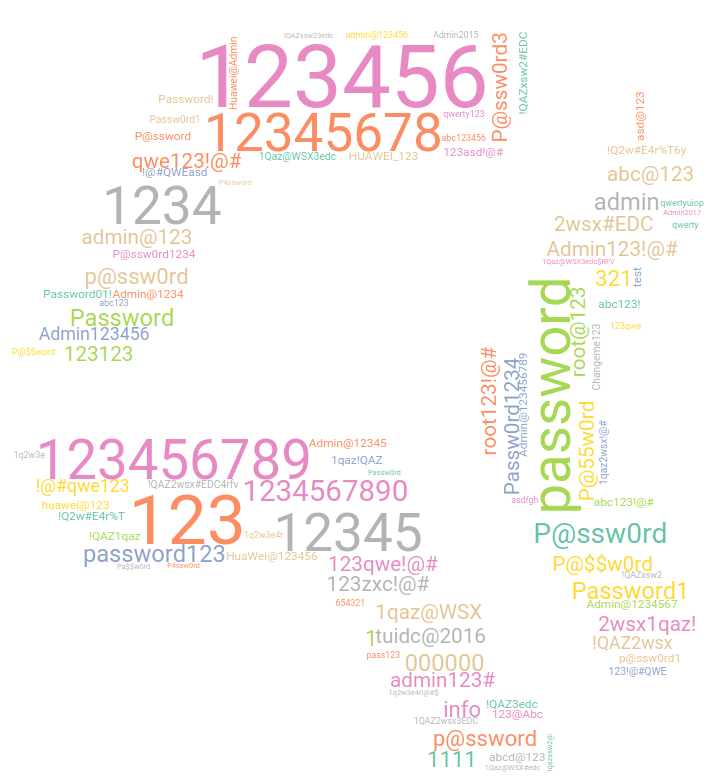
Sentinel View report – June 2023
The total number incidents decreased by half. However, there are only slightly fewer than 10,000 distinct attackers on the greylist. The last month’s seemingly minor reduction may have been indicative of an ongoing decline.
New Netmetr is called LibreSpeed and it is global
A long time ago, CZ.NIC started a project called Netmetr, which was performed in cooperation with the Czech Telecommunication Office (CTU). The goal was to provide a reliable Internet connectivity benchmark that ordinary people can use to verify the parameters of their Internet connection. The cooperation went well and CTU was getting more and more interesting data about the quality of Internet connectivity in the Czech
Republic. Moreover, CTU decided to integrate the service into their systems and maintain it by themselves. They used the open-source software Netmetr and created Nettest – their own instance integrated into their environment. That unfortunately meant that the Netmetr itself lost its main purpose and it no longer made sense to keep it running.
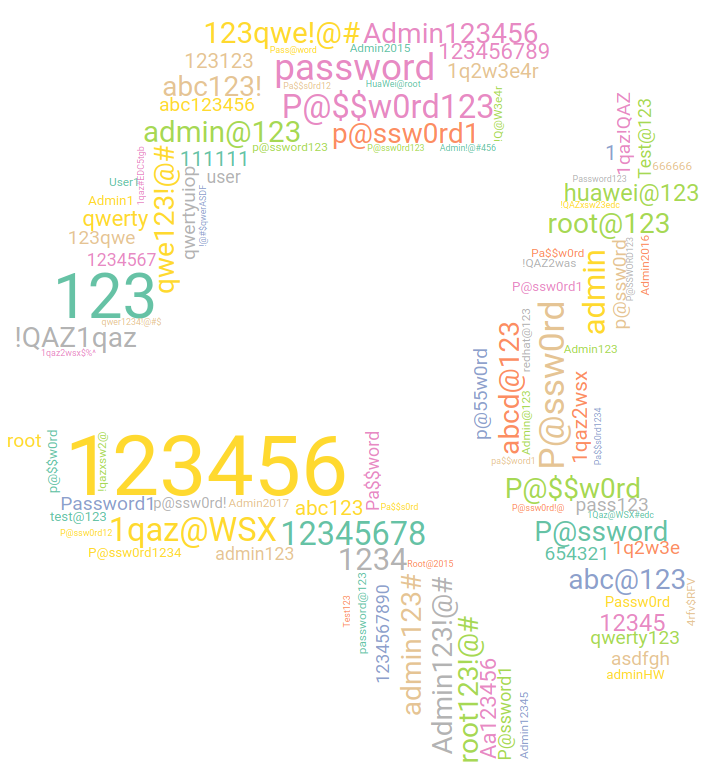
Sentinel View report – February 2023
In February, we saw about a 10% decrease in the number of unique attackers, but they were more active. Usually, we see attackers come and go, but in February, although it was fewer attackers in total, we had on average, more attackers blocked every day. This means that those attackers stayed active longer than in January.